Overview
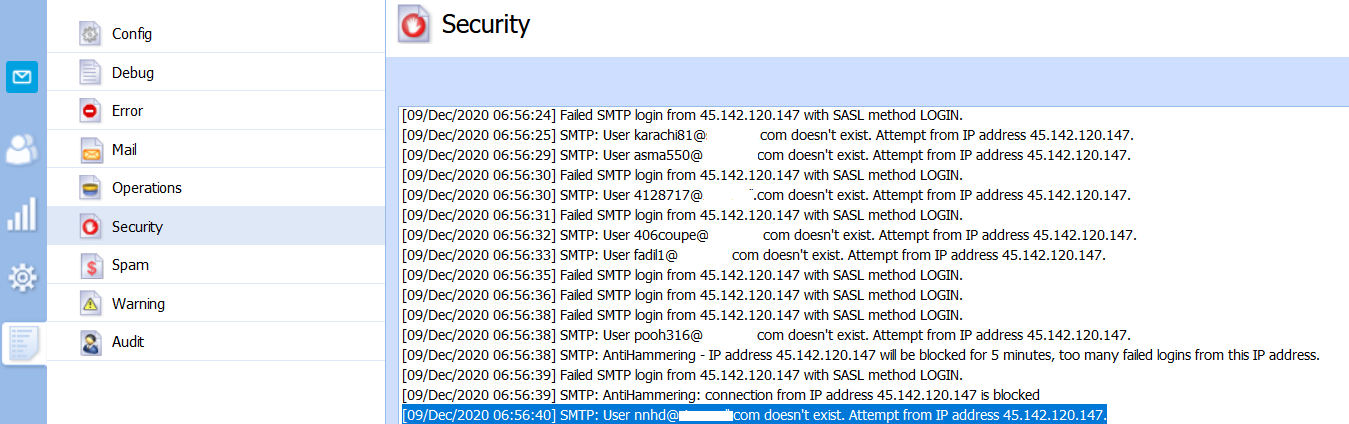
While Kerio Connect server is located behind Kerio Control (connected to the LAN interface), the Connect Security logs report unusual IP addresses trying to access the mail server or guess user passwords:
SMTP: User nnhd@domain.com doesn't exist. Attempt from IP address 45.142.120.147.
SMTP: Authentication attempt from host x.x.x.x denied, insecure authentication not allowed
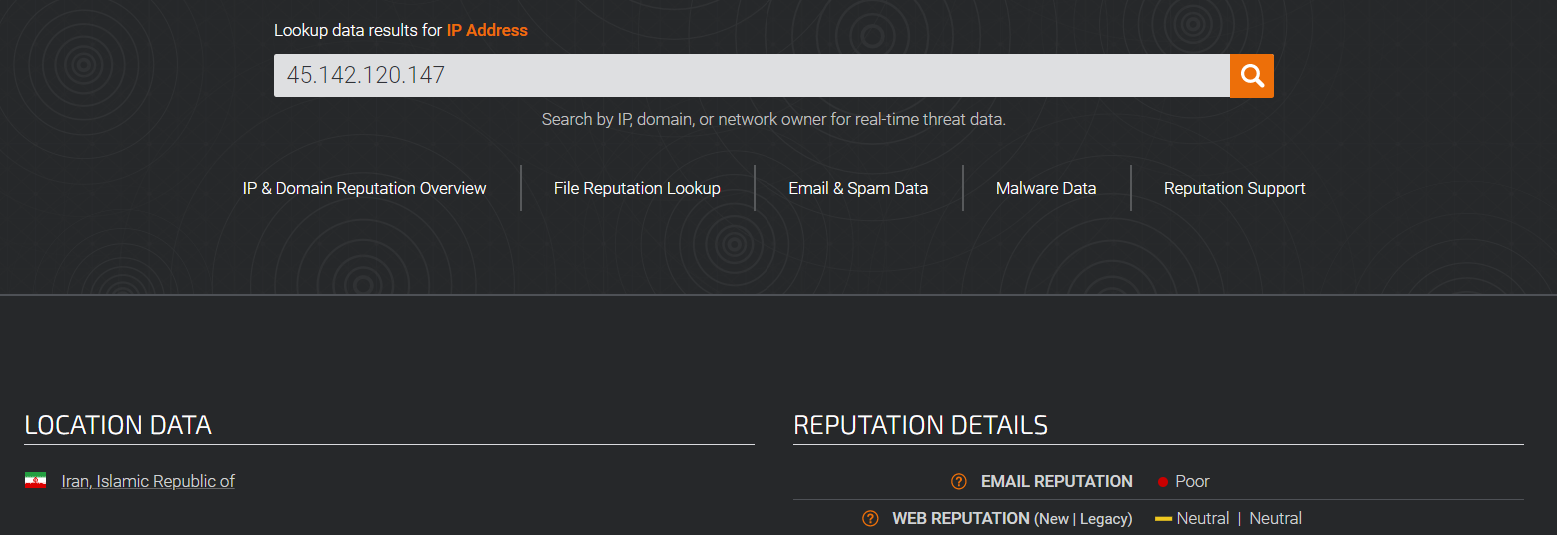
While checking the reported IP reputation scores, it shows a Poor rating.
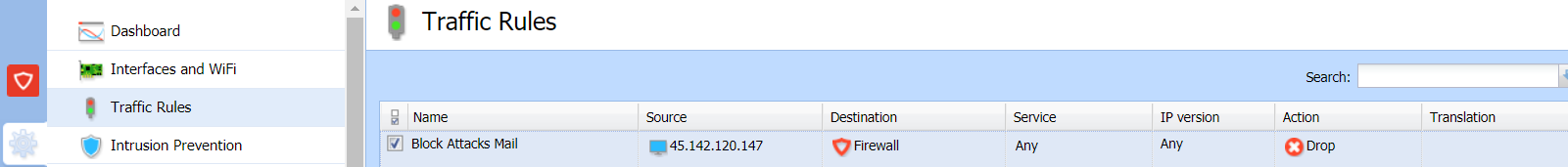
These spammers' IP addresses can be rejected by Kerio Control traffic rules.
Solution
In Kerio Control Webadmin, create a separate traffic rule with the following data:
Source: <IP_addresses_reported_in_Connect_logs>
Destination: Firewall
Service: Any
Action: Drop
Note: 45.142.120.147 is just an example here.
Testing
Kerio Connect Security log does not report any SMTP authentication attempts any more. The packets are being dropped by the Kerio Control firewall. Debug logs with "Packets dropped for some reason" show the following:
{pktdrop} packet dropped: Traffic rule: Block Attacks Mail (from Ethernet 3, proto: TCP, len 60,
45.142.120.147:18874 -> 192.168.100.10:25, flags:[ SYN ], seq:3660268187 ack:0, win:29200, tcplen:0
Priyanka Bhotika
Comments