Overview
You can create a secure tunnel between two LANs secured by a firewall (site to site VPN tunnel). This article describes creating an IPsec VPN tunnel between Kerio Control and another device, such as Fortinet, Cisco, Mikrotik, Sophos or Azure VPN. Both endpoints should be able to communicate automatically.
If a problem occurs and you have to set the values manually, consult the following tables for default and supported values in Kerio Control. The other devices may have specific requirements to work (for example Azure VPN), so you will need to fine-tune each of the endpoints based on the specific requirement. Remote endpoints of the tunnel can also use the recommended values.
Important: NAT over a Site-to-Site IPsec VPN connection is not supported.
Solution
- Modify the
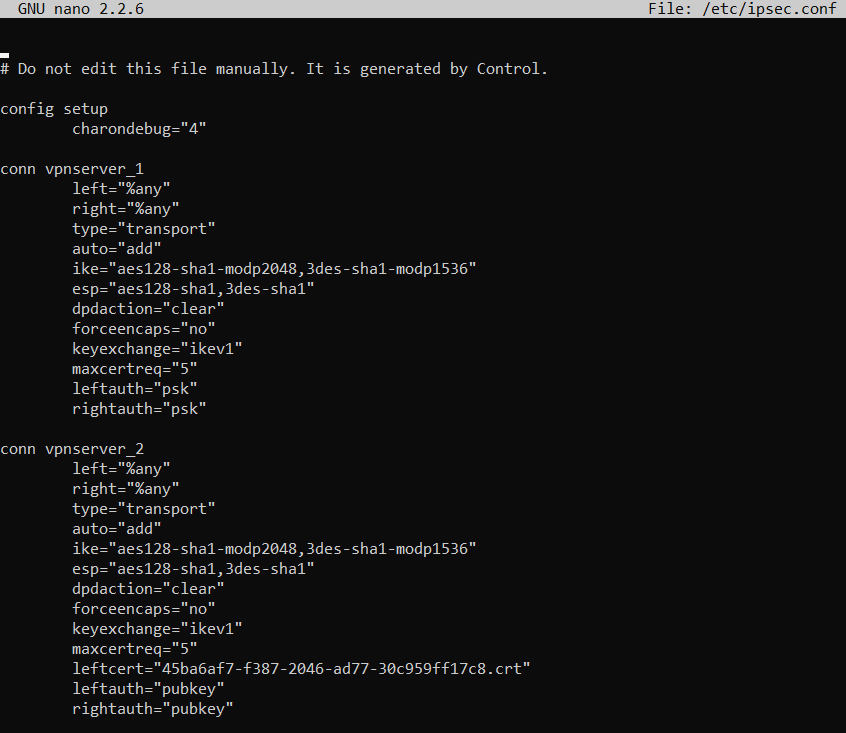
/etc/ipsec.confto set the custom Phase 1 and Phase 2 values. For more information about modification, please review Modifying Internal configuration files.
Phase 1 (IKE):
| Variable | Default values | Supported values |
Unsupported values |
|---|---|---|---|
|
Mode |
Main | NA | Aggressive |
| Remote ID type | hostname | IP address |
NA |
|
NAT Traversal |
enabled | NA | NA |
|
Ciphersuite (policies) |
aes128-sha1-modp2048,3des-sha1-modp1536 |
NA | NA |
|
Version |
IKEv1, IKEv2 | NA | NA |
|
DPD Timeouts |
enabled (30 sec) | NA | NA |
|
Lifetime |
3 hours | NA | NA |
Phase 2 (ESP):
| Variable |
Supported Values |
Unsupported Values |
|---|---|---|
|
Mode |
Tunnel | Transport |
|
Protocol |
ESP | AH |
|
Ciphersuite (policies) |
aes128-sha1, 3des-sha1 | NA |
|
PFS |
off | NA |
|
Lifetime |
60 mins | NA |
Supported ciphers
Each cipher consists of three parts:
- Encryption Algorithm — for example,
aes128 - Integrity Algorithm — for example,
sha1 - Diffie Hellman Groups — for example,
modp2048
- Set ciphers to custom values in the Kerio Control Administration -> Configuration -> Interfaces -> IPsec VPN tunnel properties (Change button).
Kerio Control supports the following ciphers:
Phase 1 (IKE) - supported ciphers
| Encryption Algorithms |
Integrity Algorithms |
Diffie Hellman Groups |
|---|---|---|
|
|
|
Phase 2 (ESP) - supported ciphers
| Encyption Algorithms |
Integrity Algorithms |
Diffie Hellman Groups |
|---|---|---|
|
|
|
Testing
The custom configuration is reflected in /etc/ipsec.conf file.
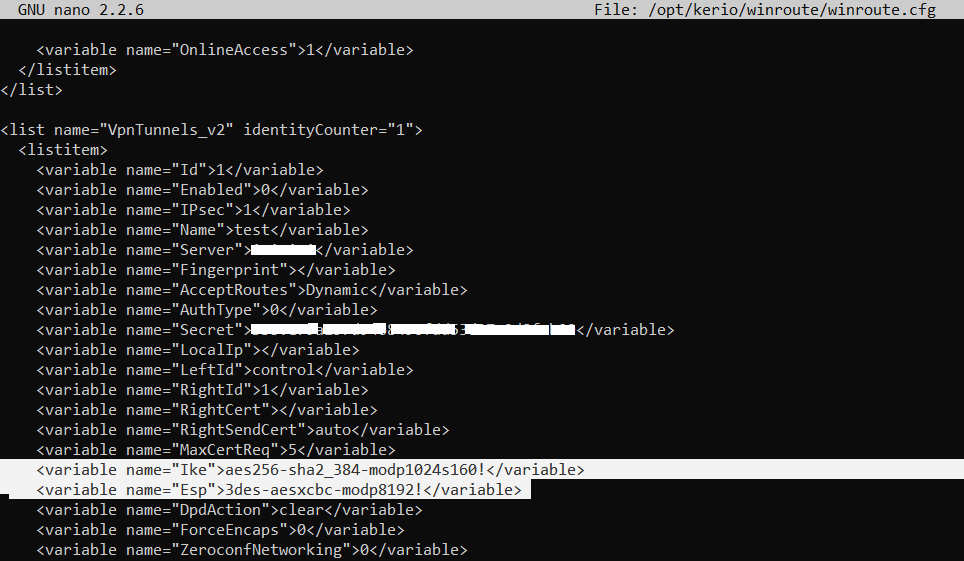
The custom IPSec VPN tunnel ciphers are in place in /opt/kerio/winroute/winroute.cfg file.

Priyanka Bhotika
Comments